Mailing list
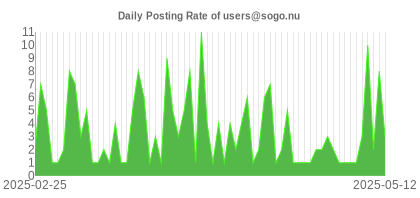
Community support is offered through the mailing list. You can subscribe to it and ask questions related to SOGo.
-
Register (free)
- visit the mailing list web site
- or send an email to users-request@sogo.nu with SUBSCRIBE users as the subject.
- Search if question has been answered
Online archives of the mailing list are available from :
https://www.mail-archive.com/users@sogo.nu/ - Ask question
Once subscribed, write to users@sogo.nu to post to the mailing list.
The SOGo community is very large and active so do not hesitate to subscribe to the mailing list and ask questions. However, please make sure to respect the following guidelines when posting a new message :
- post constructive emails - rants will be automatically discarded
- consult the FAQ for previously answered questions
- send plain text message (no HTML or Rich Text) to avoid getting rejected by our spam filters
- avoid replying to a message on top of the quoted text of the previous correspondence
Consulting Services
Groupware deployment projects are complex in nature because they usually involve many different technologies. We have done hundreds of large-scale deployment projects for prestigious organizations, all around the world. Let us help you make this deployment project a success by using our unmatched expertise!
If you are looking for a SOGo expert to help you:
- Install, configure, customize and optimize the solution to meet your needs
- Perform a pre or post-implementation audit to make sure your SOGo deployment performs optimally
- Correct a specific issue with your installation or with components related to it
- Migrate calendars, address books and emails from a previous solution to SOGo
- Efficiently integrate SOGo with in-house systems (CRM, ERP, portal, etc.)
- Develop specific features mentioned in the roadmap, vertical to your environment or others
Support Packages
| Bronze |
Silver |
Gold |
Platinum |
|
|---|---|---|---|---|
| Duration | 1 year prepaid contract. Unused tickets are not prolonged. | |||
| Support Method | Support Portal | Support Portal / Phone | Support Portal / Phone | Support Portal / Phone |
| Response Time | 1 business day | 4 business hours | 2 business hours | 1 business hour |
| Support Hours | Office Hours | Office Hours | Office Hours | Office Hours |
| Notifications | None | Security | Security / Bug Fixes | Security / Bug Fixes |
| Bug Fixes | No | No | No | Yes |
| Included Incidents | 5 | 10 | 30 | 75 |
| Included Consulting Hours | - | - | 4 | 8 |
| Cost | 500 € | 1,500 € | 5,000 € | 7,500 € |
| Order | Order | Order | Order | |
Supported operating systems:
- CentOS 7 / 8
- Red Hat Enterprise Linux (RHEL) 7 / 8 / 9
- Debian 8 to 12
- Ubuntu 14 to 24
The support packages do not include:
- components installation
- custom development
- preventive system monitoring
- training and documentation
The included consulting hours can be consumed for:
- architecture design and review
- migration from another system
- performance tuning
- best practices
Documentation
FAQ
How to use WebAuth with SOGo?
When using proxy-side authentication, you must adjust your proxy or front server accordingly and ensure that the “x-webobjects-remote-user” HTTP header is passed to SOGo. With Apache, this is done by using the “RequestHeader” directive in the configuration. The second step is to tell SOGo to trust that value altogether by setting the “SOGoTrustProxyAuthentication” to YES which will disable the login page and the “logoff” link. If the user identifiers that are used do not match their system identifier, for example using Kerberos-based authentication, you need to set the “bindFields” parameter of your authentication LDAP source. This enables SOGo to query your LDAP server for the real user identifier to use during its operations.
Bug Tracking System
If you encounter a possible bug with SOGo, you can access our bug tracking system.
By default you will have the viewer rights, but you need to contact us to upgrade your account to report issues (the procedure is detailed on the bug tracker).
Please make sure to respect the following guidelines when reporting a bug:
- verify that the bug you found is not already known or even fixed in the trunk version
- make the actual facts very clear; be precise, we need to be able to reproduce the problem
- explain your speculations, if any
- add a screenshot to the ticket if appropriate