Mailing list
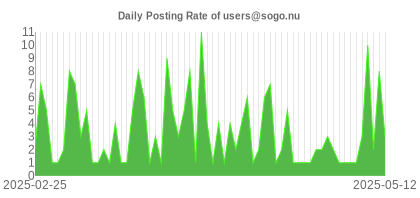
Community support is offered through the mailing list. You can subscribe to it and ask questions related to SOGo.
-
Register (free)
- visit the mailing list web site
- or send an email to users-request@sogo.nu with SUBSCRIBE users as the subject.
- Search if question has been answered
Online archives of the mailing list are available from :
https://www.mail-archive.com/users@sogo.nu/ - Ask question
Once subscribed, write to users@sogo.nu to post to the mailing list.
The SOGo community is very large and active so do not hesitate to subscribe to the mailing list and ask questions. However, please make sure to respect the following guidelines when posting a new message :
- post constructive emails - rants will be automatically discarded
- consult the FAQ for previously answered questions
- send plain text message (no HTML or Rich Text) to avoid getting rejected by our spam filters
- avoid replying to a message on top of the quoted text of the previous correspondence
Consulting Services
Groupware deployment projects are complex in nature because they usually involve many different technologies. We have done hundreds of large-scale deployment projects for prestigious organizations, all around the world. Let us help you make this deployment project a success by using our unmatched expertise!
If you are looking for a SOGo expert to help you:
- Install, configure, customize and optimize the solution to meet your needs
- Perform a pre or post-implementation audit to make sure your SOGo deployment performs optimally
- Correct a specific issue with your installation or with components related to it
- Migrate calendars, address books and emails from a previous solution to SOGo
- Efficiently integrate SOGo with in-house systems (CRM, ERP, portal, etc.)
- Develop specific features mentioned in the roadmap, vertical to your environment or others
Support Packages
| Bronze |
Silver |
Gold |
Platinum |
|
|---|---|---|---|---|
| Duration | 1 year prepaid contract. Unused tickets are not prolonged. | |||
| Support Method | Support Portal | Support Portal / Phone | Support Portal / Phone | Support Portal / Phone |
| Response Time | 1 business day | 4 business hours | 2 business hours | 1 business hour |
| Support Hours | Office Hours | Office Hours | Office Hours | Office Hours |
| Notifications | None | Security | Security / Bug Fixes | Security / Bug Fixes |
| Bug Fixes | No | No | No | Yes |
| Included Incidents | 5 | 10 | 30 | 75 |
| Included Consulting Hours | - | - | 4 | 8 |
| Cost | 500 € | 1,500 € | 5,000 € | 7,500 € |
| Order | Order | Order | Order | |
Supported operating systems:
- CentOS 7 / 8
- Red Hat Enterprise Linux (RHEL) 7 / 8 / 9
- Debian 8 to 12
- Ubuntu 14 to 24
The support packages do not include:
- components installation
- custom development
- preventive system monitoring
- training and documentation
The included consulting hours can be consumed for:
- architecture design and review
- migration from another system
- performance tuning
- best practices
Documentation
FAQ
How do I debug SOGo?
Prerequisites
First, make sure you’ve installed the debugging symbols for GNUstep, SOGo and SOPE. On RHEL-based distributions, debugging symbols will be located in packages with the “debuginfo” suffix, while on Debian-based distributions, the suffix is “dbg” or “dbgsym”.
Redhat Enterprise Linux
On RHEL-based distributions, proceed with the following command:
yum install sogo-debuginfo sope49-debuginfo gnustep-base-debuginfo
Debian and Ubuntu
For Debian Stretch/9.0, you must first append a new repository to /etc/apt/sources.list:
deb http://deb.debian.org/debian-debug/ stretch-debug main
For Debian Buster/10.0, you must first append a new repository to /etc/apt/sources.list:
deb http://deb.debian.org/debian-debug/ buster-debug main
For Ubuntu, you must first add dbg symbols repository:
echo "deb http://ddebs.ubuntu.com $(lsb_release -cs) main restricted universe multiverse
deb http://ddebs.ubuntu.com $(lsb_release -cs)-updates main restricted universe multiverse
deb http://ddebs.ubuntu.com $(lsb_release -cs)-proposed main restricted universe multiverse" | \
tee -a /etc/apt/sources.list.d/ddebs.list
apt install ubuntu-dbgsym-keyring
apt-key adv --keyserver keyserver.ubuntu.com --recv-keys F2EDC64DC5AEE1F6B9C621F0C8CAB6595FDFF622
You can now update your packages index and install the packages:
apt-get update
apt-get install libgnustep-base*-dbg* sogo-dbg sope4.9-dbg gdb
Using gdb
If you’re only interested in debugging SOGo, make sure it’s first stopped and no “sogod” process is running.
Then, change to the SOGo user and launch SOGo inside gdb:
% su -s /bin/bash - sogo
% gdb --args /usr/sbin/sogod -WOUseWatchDog NO -WONoDetach YES -WOPort 127.0.0.1:20000 -WOWorkersCount 1 -WOLogFile - -WOPidFile /tmp/sogo.pid
Launch the application using the “run” command (or “r”). This will start SOGo using a single process inside gdb.
Once SOGo is launched, hit Control-C and set breakpoints, like this:
(gdb) b [NSException raise]
Breakpoint 1 at 0x7ffff5241d90: file NSException.m, line 955.
(gdb) b abort
Breakpoint 2 at 0x7ffff5352f50: abort. (2 locations)
Resume’s SOGo state, putting it back into a running one:
(gdb) c
Continuing.
When the application is about to crash, your breakpoints should be raised:
Breakpoint 1, -[NSException raise] (self=0x55555611fe20, _cmd=0x7ffff56f5f00) at NSException.m:955
(gdb)
At this point, you can produce a back trace using the “bt” command:
(gdb) bt
#0 -[NSException raise] (self=0x55555611fe20, _cmd=0x7ffff56f5f00) at NSException.m:955
#1 0x00007ffff5242231 in +[NSException raise:format:] (self=0x7ffff56f6080, _cmd=<optimized out>, name=0x7ffff56f6220,
format=0x7ffff56c57f0) at NSException.m:835
#2 0x00007ffff51b8e89 in characterAtIndex_c (index=306, self=<optimized out>) at GSString.m:1199
#3 -[GSMutableString characterAtIndex:] (self=0x555555878630, _cmd=<optimized out>, index=<optimized out>) at GSString.m:3797
#4 0x00007ffff7b73185 in -[NSString(SOGoURLExtension) _rangeOfURLInRange:] (self=0x555555878630, _cmd=0x7ffff7dc9e00, refRange=...)
at NSString+Utilities.m:133
#5 0x00007ffff7b73732 in -[NSString(SOGoURLExtension) _handleURLs:textToMatch:prefix:inRanges:] (self=0x55555610bbf0, _cmd=0x7ffff7dc9ec0,
selfCopy=0x555555878630, match=0x7ffff7dc9240, prefix=0x7ffff7dc9260, ranges=0x555555878b70) at NSString+Utilities.m:202
#6 0x00007ffff7b73c49 in -[NSString(SOGoURLExtension) stringByDetectingURLs] (self=0x55555610bbf0, _cmd=0x7fffea5b6c80)
at NSString+Utilities.m:258
#7 0x00007fffea3a8537 in -[UIxMailPartTextViewer flatContentAsString] (self=0x555556056070, _cmd=0x5555562d6e00)
at UIxMailPartTextViewer.m:48
You can also attach to a running sogod process using gdb. For example, if a sogod process is consuming 100% and its PID is 1234, you can attach to it using “gdb -p 1234”. At this point, you can also produce back traces (“bt” or “bt full”), put the process back in the running state (“c”) or interrupt it (Control-C).
Next thing is to file a detailed bug on http://sogo.nu/bugs.
Bug Tracking System
If you encounter a possible bug with SOGo, you can access our bug tracking system.
By default you will have the viewer rights, but you need to contact us to upgrade your account to report issues (the procedure is detailed on the bug tracker).
Please make sure to respect the following guidelines when reporting a bug:
- verify that the bug you found is not already known or even fixed in the trunk version
- make the actual facts very clear; be precise, we need to be able to reproduce the problem
- explain your speculations, if any
- add a screenshot to the ticket if appropriate